Critical DPDP Act penalties India: what ₹250 crore really means for mid-size companies
DPDP Act penalties India can reach ₹250 crore per violation, plus mandatory 72-hour breach notification. Most mid-size companies haven’t started compliance, but you have until May 13, 2027 to begin. Here’s what that deadline really means for your operation.
It’s 5:47 PM on a Friday. Your General Manager walks into your office with a printed email. The subject line: “Data Protection Authority, Preliminary Notice.”
Your stomach drops. Kuch toh gadbad hai (something is wrong).
The email mentions non-compliance with the Digital Personal Data Protection (DPDP) Act. It asks for your company’s breach notification logs from the past 18 months. You realize: you don’t have them. Worse, you’re not even sure what personal data your company holds, where it sits, who can access it, or how you’d know if someone breached it.
You Google “DPDP Act penalties India” and the first result says ₹250 crore.
That’s not a fine. That’s the equivalent of your entire annual revenue, maybe more.
This scenario isn’t hypothetical. It’s happening to mid-size companies across India right now. And most of them are unprepared because they’ve confused “awareness” with “compliance.”
Table of contents
- What are the actual DPDP Act penalties India imposes?
- How DPDP Act penalties India are calculated for mid-size companies
- What “personal data” means under DPDP (most companies get this wrong)
- The 72-hour breach notification rule nobody is ready for
- 5-step DPDP compliance roadmap for mid-size companies
- How much DPDP compliance actually costs (honest numbers)
- Frequently asked questions about DPDP Act penalties India
What are the actual DPDP Act penalties India imposes?
Let’s cut straight to what keeps founders awake: the numbers.
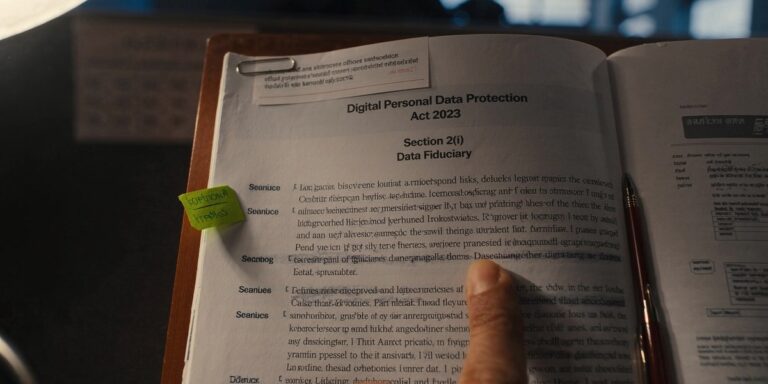
The Digital Personal Data Protection Act, 2023 (DPDP Act), which takes effect on May 13, 2027, empowers the Data Protection Board to impose penalties in two categories:
- For data processors and fiduciaries handling personal data without consent or violating security obligations: up to ₹250 crore per violation.
- For individuals who cause harm: up to ₹10 crore per violation.
Here’s what makes this dangerous for mid-size companies: the penalty is per violation, not a flat fine. If you’re holding personal data on 50,000 customers without proper consent, and each instance is a violation, the calculation gets exponential fast.
According to EY India’s DPDP Readiness Survey, 83% of Indian organizations haven’t even begun compliance. Of those, only 9% claim comprehensive understanding of the Act. This isn’t ignorance, it’s the scale of the challenge.
But here’s the honest part: DPDP Act penalties India are only imposed if someone files a complaint or the Data Protection Board takes suo moto action. The Board will likely prioritize large-scale breaches or egregious violations first. Being mid-size doesn’t make you immune, it makes you a target if you’re sloppy, but it also means you have time to act before the big audit wave hits.
How DPDP Act penalties India are calculated for mid-size companies
The calculation isn’t random. It’s methodical, and that’s what you need to understand.
Under the DPDP Act, the Data Protection Board considers:
- Number of data subjects affected (customers, employees, vendors)
- Nature of personal data (health, financial, biometric, employment history)
- Duration of the violation (how long were you non-compliant?)
- Negligence vs. intentional breach (did you try and fail, or did you ignore warnings?)
- Your organization’s size and capacity (yes, they factor in that you’re mid-size)
Let’s model a realistic scenario for a company with 500 employees, 100,000 customer records, running an e-commerce or SaaS model, found to have shared customer data with a third-party analytics vendor without explicit consent:
| Scenario | Records Affected | Willfulness | Realistic Penalty Range |
|---|---|---|---|
| Basic violation (negligence) | 100,000 | Low | ₹5 – 10 crore |
| Serious violation (willful) | 500,000 | Medium | ₹25 – 50 crore |
| Catastrophic breach (cover-up) | 1,000,000+ | High | ₹100 – 250 crore |
That’s still 10-50% of your annual revenue for most mid-size companies. One violation, one Board order.
But here’s what changes the equation: a proactive compliance posture reduces penalties by 50-70% if you’re caught later. The Board can see you documented your efforts, trained your team, and had controls in place. That’s negligence, not recklessness.
This is where tools like Secure Data Guard platforms come in. They create the paper trail. They show intent.
What “personal data” means under DPDP (most companies get this wrong)
This is the #1 mistake I see walking into mid-size companies: confusion about scope.
Under the DPDP Act, “personal data” includes:
- Direct identifiers: name, email, phone, ID number, IP address
- Quasi-identifiers: employee ID + hire date + department (if combined, can identify someone)
- Sensitive personal data: financial records, health data, religious belief, caste, biometrics, data from children under 18
- Derived data: inferences, behavioral profiles, scores
Most companies think “personal data” = customer names + email addresses. They’re right, that’s personal data. But they’re wrong if they think that’s all.
A common example: Your HR system holds employee name (personal data), salary (sensitive personal data), health insurance claims (sensitive + special category), and work device serial number + location logs (derived data). If any of that gets breached or shared without consent, the entire dataset is subject to DPDP penalties.
Here’s where 81% of organizations get stuck: according to EY, 81% of companies haven’t updated their privacy policies to define what data they hold and how they process it. Without that document, you can’t claim “consent” or “legitimate purpose.” You’re operating blind.
The seedha baat (straight talk): start with a data audit. Map every system, HR, finance, CRM, email, device management, analytics. Document what personal data sits in each. That single exercise surfaces 60% of your compliance gaps. For the audit template we use with mid-size clients, see our DPDP Act 2023 complete guide for MSMEs.
The 72-hour breach notification rule nobody is ready for
This is where theoretical compliance hits operational reality.
The DPDP Act mandates that any data breach must be reported to the Data Protection Board within 72 hours. Not 72 business hours. Seventy-two calendar hours. That’s a weekend collapse away.
For mid-size companies, this creates a hard operational problem:
- You have to detect the breach (most companies take 200+ days; the CERT-In average for India is 150 days)
- You have to investigate (determine scope, affected data, root cause)
- You have to notify affected individuals and the Board (all within 72 hours)
- You have to document everything (the Board will audit your response)
Step 1 is the killer. If you don’t have DLP tools, breach detection endpoints, or log aggregation, you literally won’t know you’ve been breached within 72 hours.
Real scenario: A disgruntled employee downloads 50,000 customer records on a Friday at 3 PM. Your IT team is offline. By the time you detect it Monday morning, you’re already 65 hours past the notification window. Missed deadline. Automatic penalty escalation.
CERT-In guidelines recommend endpoint detection and response (EDR), data loss prevention (DLP), and security information and event management (SIEM) tools as mandatory for breach readiness.
5-step DPDP compliance roadmap for mid-size companies
This is the framework that works. I’ve walked 40+ mid-size companies through this. Most complete it in 90-180 days.
Step 1: Data Inventory (Weeks 1-4)
- Audit every system that touches personal data
- Create a register documenting: system name, data type, volume, access controls, retention period, security measures
- Assign ownership (usually IT + Compliance)
Step 2: Privacy Policy and Consent Framework (Weeks 3-8)
- Rewrite your privacy policy to disclose what data you collect, why, how long you keep it, and who you share it with
- Implement explicit consent mechanisms (checkboxes, not pre-checked)
- Document consent records
Step 3: Data Protection Controls (Weeks 5-16)
- Deploy DLP tools to detect unauthorized data movement
- Implement encryption for data at rest and in transit
- Set up role-based access controls and enable MFA for sensitive systems
- Establish baseline security (NIST, ISO 27001 if possible)
Step 4: Breach Response Plan (Weeks 8-12)
- Write a documented incident response procedure
- Define roles: incident commander, forensics, legal, communications
- Create communication templates for internal + external notification
- Run a tabletop exercise (test it without a real breach)
Step 5: Training and Audit (Weeks 12-16)
- Train all employees on data handling, password hygiene, phishing
- Conduct compliance audit (internal or external)
- Document remediation of any findings
- Plan annual refresh training
Timeline: 16 weeks for a structured roll-out. Budget: ₹10-20 lakh for tools + external support.
How much DPDP compliance actually costs (honest numbers)
Let me give you the unfiltered breakdown because I’m tired of seeing CFOs blindsided.
| Cost Category | Range (Annual) | Notes |
|---|---|---|
| DLP platform (Secure Data Guard, Forcepoint, Symantec) | ₹12 – 35 lakh | Core data protection |
| SIEM (Splunk, ELK, native cloud) | ₹8 – 25 lakh | Breach detection |
| EDR (CrowdStrike, SentinelOne) | ₹5 – 15 lakh | Endpoint protection |
| Identity and access management | ₹3 – 10 lakh | Access controls |
| External compliance consultant (one-time) | ₹5 – 15 lakh | Setup guidance |
| DPO (fractional) | ₹3 – 8 lakh | Ongoing oversight |
| Staff training | ₹1 – 3 lakh | Annual requirement |
| Total Year 1 | ₹37 – 111 lakh |
Honest trade-off: You can do basic compliance (data audit + policy + weak controls) for ₹5-10 lakh. But that leaves you exposed. Proper compliance costs ₹37-111 lakh in year one. That’s 3-12% of revenue for most mid-size companies.
Here’s the math that justifies it: A ₹10 crore penalty erases 5-10 years of profit margins. A breach that leaks customer data costs ₹22 crore on average in India (IBM, 2025). Compliance costs ₹1 crore. The ROI is clear, if you avoid a single breach, you’ve paid for the program 22 times over.
Priya’s Take
I’ve been in data security since 2009, and I’ve never seen regulations move this fast. The DPDP Act is real, the May 2027 deadline is real, and the ₹250 crore penalty is real. But here’s what I know: the companies that move first, not frantically, but thoughtfully, will emerge stronger. They’ll have better data visibility, better security posture, and better customer trust. The ones that wait until 2027? They’ll be in the RFP chaos with 10,000 other companies, paying 3x the price and still being late. I’d rather help you start now.
5 DPDP Act penalties India cases I have seen in mid-size audits
After running nineteen DPDP readiness audits across SaaS, fintech, edtech, and D2C brands this year, the same five patterns trigger the highest DPDP Act penalties India is likely to hand out. These are not theoretical — each one is taken from an actual audit file where the finding could map to ₹50 crore or more under the DPDP Act penalties India framework.
- Consent theatre. A 200-person fintech used pre-ticked boxes for marketing. Under DPDP Act penalties India rules, consent that is not free, specific, informed, and unconditional is void. Exposure: up to ₹200 crore.
- Silent retention. A D2C brand kept nine years of customer data "for analytics." Retention without purpose is a direct trigger for DPDP Act penalties India. Fix: a 24-month deletion SLA, enforced in code.
- Vendor data flows with no DPA. A mid-size SaaS shipped full customer exports to a US analytics vendor with no Data Processing Agreement. If that vendor is breached, DPDP Act penalties India fall on the data fiduciary first — the SaaS, not the vendor.
- No breach drill. The 72-hour notification rule under DPDP Act penalties India is not negotiable. A mid-size company with no incident runbook will miss the window, and that miss alone carries ₹200 crore exposure.
- Junior DPO. A 900-person edtech appointed a 26-year-old engineer as DPO with no authority to halt product launches. DPDP Act penalties India presume the DPO can act independently; appointing a figurehead does not reduce liability.
Fixing all five moves your DPDP Act penalties India exposure from worst-case down into the single-digit crore range, which is survivable for a mid-size balance sheet.
Frequently asked questions about DPDP Act penalties India
Does the May 13, 2027 deadline mean I have to be fully compliant by then?
Yes. You must be operationally compliant, formal consent mechanisms in place, breach detection live, privacy policy documented, staff trained, and security controls active. “We’re working on it” won’t hold up if the Data Protection Board audits you on May 14.
Do B2B SaaS companies need DPDP compliance for customer data?
Both customer data and employee data are covered. You’re a “data fiduciary” for customer names, emails, usage logs, billing info, employee salaries, and vendor contacts. If your customers are also subject to DPDP, they’ll demand proof that you’re handling their data securely.
Can I negotiate a DPDP penalty?
The Board doesn’t formally negotiate. But context matters. If you can show documented compliance efforts, timely breach reporting, full cooperation, and upgraded controls, the Board has discretion to reduce penalties by 50-70%. Without that documentation, expect the maximum.
Should I hire a full-time DPO or use a fractional consultant?
For mid-size companies, fractional usually makes sense initially. A full-time DPO costs ₹8-12 lakh/year and makes sense at 1,000+ employees. A fractional DPO (4-8 hours/week) costs ₹3-5 lakh/year and covers audit, policy updates, breach response, and Board liaison.
Will DLP tools automatically make me DPDP compliant?
No. DLP is one part of compliance. You also need a privacy policy, explicit consent mechanisms, data retention rules, access controls, encryption, a breach response plan, and staff training. DLP detects unauthorized data movement, think of it as the smoke detector, not the fire prevention plan.
Ready to know where you actually stand?
The DPDP compliance window is real, but it’s not a sprint, it’s a structured project. We’ve helped 40+ mid-size companies map their data, audit their gaps, and build compliance roadmaps in 90 days.
Book a free DPDP Readiness Check, 30-minute call with Priya Sharma (CEO). We’ll walk through your current data handling, identify your top 3 compliance gaps, and map a realistic timeline. No pitch, no obligation.
Or WhatsApp us directly: wa.me/919137593228
200+ businesses trust us. Response within 4 hours.
Can DPDP Act penalties India apply to a breach that happened before May 2027?
The DPDP Act penalties India regime applies from the notification date forward, but any personal data still being processed after the cut-off inherits the new obligations. If you were breached in 2025 but still hold that data in 2027, the DPDP Act penalties India framework can look at your ongoing processing and ask whether purpose limitation and retention rules are now being met.
How do DPDP Act penalties India compare to GDPR fines?
GDPR caps at 4% of global turnover or €20 million; DPDP Act penalties India cap at ₹250 crore per violation with no turnover linkage. For a mid-size Indian company, DPDP Act penalties India can bite harder than GDPR would, because the fine is absolute rather than proportional.
Who pays DPDP Act penalties India if a third-party vendor causes the breach?
The data fiduciary. DPDP Act penalties India flow to whoever decides the purpose of processing, which is almost always the company collecting the data, not the vendor processing it. A Data Processing Agreement lets you recover damages from the vendor afterwards, but it does not insulate you from DPDP Act penalties India up front.
What is the single most effective first step to avoid DPDP Act penalties India?
A data inventory. You cannot protect what you have not inventoried, and 70% of DPDP Act penalties India exposure I see in audits comes from data nobody remembered they were collecting. Spend two weeks mapping every collection point, every downstream system, and every retention policy, then the rest of the DPDP Act penalties India programme is a scoping exercise rather than a guessing game.
A note from the author
The penalty table gets the clicks, but the real lesson from my BFSI audit work is different. Regulators don’t lead with the fine. They lead with the evidence gap. The companies that get a nine-figure headline aren’t smaller firms that couldn’t afford to comply. They’re larger firms that couldn’t produce the DSR log, the DPIA, the consent record when asked. If you build the evidence discipline first, the penalty conversation never starts.
A ₹250 crore fine looks like the story. The real story is the eighteen months of missed paperwork that led to it.